XCP-ng Security Bulletin: multiple vulnerabilities related to PV guests
Multiple Xen Security Advisories
Here is the latest XCP-ng security bulletin. All these vulnerabilities are patched and already available in XCP-ng updates (For both XCP-ng 7.5 and 7.6)
As usual, refer to our Updates Howto for update instructions. In short, you have two options:
- using
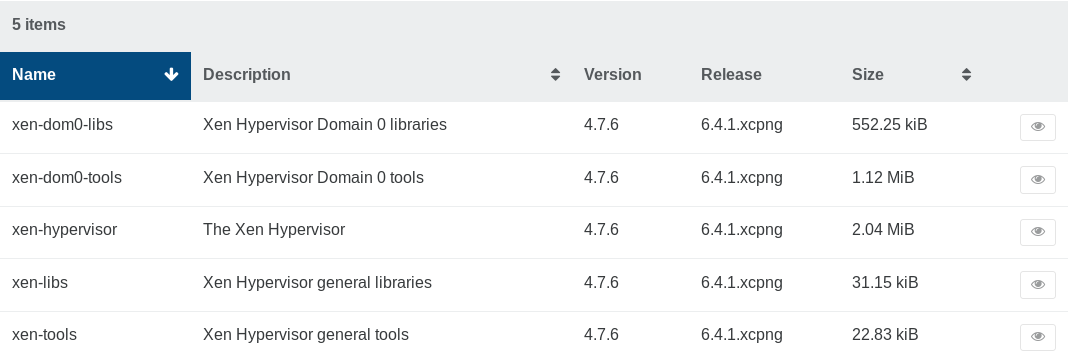
yum updatedirectly on each host - using Xen Orchestra to install them pool wide with one click in the "Patch" tab of the pool view, clicking on the "Install pool patches" button:
Note: updating won't interrupt anything, you can update confidently in production. It will take affect only after a host reboot.
It's up to you to decide when to reboot your hosts. As usual, always reboot your master first. Just be aware that until you decide to reboot, your hosts aren't protected against these attacks.

Details about the vulnerabilities
XSA-284, XSA-285, XSA-287, XSA-288, XSA-290, XSA-292, XSA-293 and XSA-294
Here is the list of vulnerabilities fixed in the latest XCP-ng updates. The official advisories are available at http://xenbits.xen.org/xsa/. We summarize them here for you.
In a nutshell, there are vulnerabilities that 32-bit and/or 64-bit x86 PV guests can leverage in some situations to compromise or crash the host. HVM and PVH guests cannot use these vulnerabilities.
Some of these Xen vulnerabilities may not entirely apply to XCP-ng systems, but they have all been patched in our Xen packages.
XSA-284
32-bit x86 PV guests can cause a memory leak, due to a bug in the code processing grant table transfer requests. "Malicious or buggy guests with passed-through PCI devices may also be able to escalate their privileges, crash the host, or access data belonging to other guests." (quoting the advisory).
Only hosts with more than 168 GiB of physical memory are vulnerable. Full advisory.
XSA-285
x86 PV guests which are assigned a passed-through PCI device after domain creation may exploit this vulnerability to escalate their privilege to that of the hypervisor. The vulnerability is due to a race condition. Full advisory.
XSA-287
Another vulnerability due to several potential race conditions. The main impact is that a single PV guest can leak arbitrary amounts of memory and thus lead to a denial of service.
With very precisely timed attacks (which may be difficult to do in practice), cooperating guests might manage to cause information disclosure or privilege escalation. Full advisory.
XSA-288
Another vulnerability where a PV guest with direct access to a physical device can achieve privilege escalation under some circumstances. Full advisory.
XSA-290
x86 PV guests can mount a Denial of Service attack affecting the whole system by managing to run operations for longer than acceptable times due to missing preemption in x86 PV page table unvalidation. Full advisory.
XSA-292 and XSA-294
Only affects XCP-ng 7.6, not XCP-ng 7.5, because the use of PCID to improve performance was not backported to this version.
Quoting the advisory: "Use of Process Context Identifiers (PCID) was introduced into Xen in order to improve performance after XSA-254 (and in particular its Meltdown sub-issue). This enablement implied changes to the TLB flushing logic.". Then they explain two aspects TLB flushing logic that had been overlooked, causing vulnerabilities that x86 PV guests can exploit (in the case of XSA-294, only 64-bit guests). Full advisories: XSA-292 and XSA-294.
XSA-293
On hardware that supports the fsgsbase feature, unprivileged userspace processes running in malicious 64-bit x86 PV guests may exploit a PV kernel context switch corruption in order to escalate their privileges to that of other userspace processes running in the same guest. Some guest software attempting to use the fsgsbase feature may also trigger the bug accidentally and lead to crashes or corruption of other processes in the same guest. Full advisory.
Reminder about risks related to hyper-threading (SMT)
We would like to remind you that since XSA-273 (L1 Terminal Fault speculative side channel), it may be recommended to disable hyper-threading depending on your situation. Read "RISK ASSESSMENT OF SMT/HYPER-THREADING".
In XSA-289 (Cache-load gadgets exploitable with L1TF), it is also recommended either to use hardware without the exploitable bug described in this advisory, or to disable hyper-threading.




