XCP-ng Security Bulletin: multiple vulnerabilities
Here is your latest XCP-ng sec bulletin, with multiple Xen Security Advisory: XSA-275, XSA-279, XSA-280 and finally XSA-282.
First things first: all those vulnerabilities are patched and already available in XCP-ng updates (for both XCP-ng 7.5 and 7.6).
As usual, 2 options to get them:
- using
yum updatedirectly on each host - using Xen Orchestra to install them pool wide in one click in the "Patch" tab of the pool view, clicking on the "Install pool patches" button:

Note: updating won't interrupt anything, you can update confidently in production. It will be taken into account only after a host reboot.
It's up to you to decide when to reboot your hosts. As usual, always reboot your master first. Just be aware that until you decide to reboot, your hosts aren't protected against those attacks.
XCP-ng security policy
We are proud to announce that XCP-ng is now officially member of the Xen Advisory pre-disclosure mailing list, for security fixes under embargo. This allow to have more time to find solutions on potential big security issues and to talk with Xen teams about that.
Note that Xen project got a very advanced and powerful security process. You can find more about it here: https://www.xenproject.org/security-policy.html. XCP-ng project can be found under the "Organizations on the pre-disclosure list" paragraph.
Finally, if you find any security issue in XCP-ng, we have a dedicated response team and a email for that: please contact security at xcp-ng dot org.
Vulnerabilities details
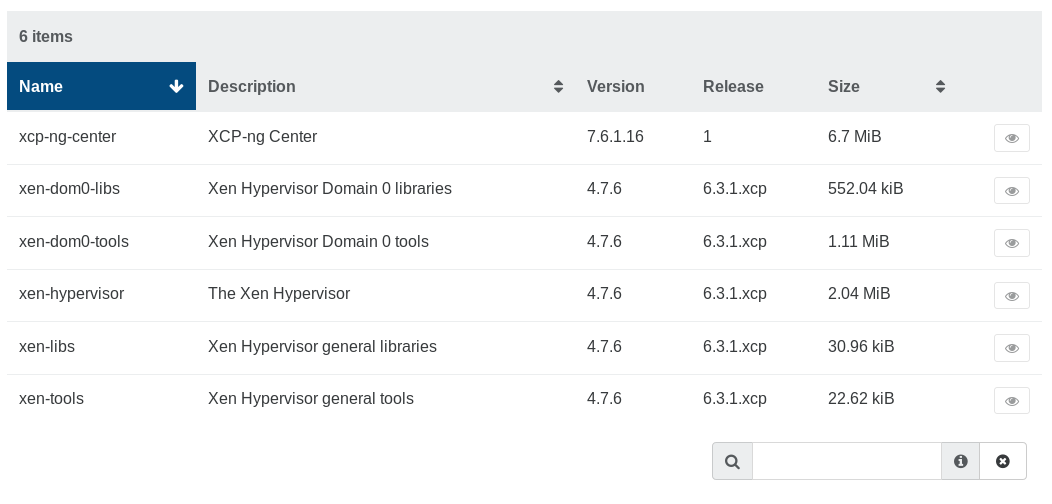
Here is the list of vulnerabilities fixed in latest XCP-ng updates.
XSA-275
XSA-275 can be sum up as an insufficient TLB flushing, and/or improper large page mappings with AMD IOMMUs. What's the impact? Well, it means a malicious guest may be able to do a privilege escalation causing the host to crash. Information leak cannot be excluded too. Only AMD users with IOMMU are vulnerable until the patch is applied. This also require PCI devices assigned to the malicious guest. Read the details here.

XSA-279
This security issue affects only 64-bits PV guest on Intel Haswell CPUs (or more recents): the root cause is an issue on a specific Intel instruction call with specific parameters that could lead to a host crash. All details here.
Fun fact: this security issue is somehow a consequence on previous security patches regarding Meltdown mitigation.
XSA-280
Only PV guests are affected by XSA-280. And like XSA-279, it's a consequence on previous security work. In this case, it's a conflict with shadow paging due to previous work on XSA-240. It affects both AMD and Intel CPUs, and can lead to host crashes. As for others XSA's, if you want to learn more about it, go read the XSA directly.
XSA-282
And at least, XSA-282 is a specific Intel issue documented officially as: "Processor May Hang When Executing Code In an HLE Transaction". In other words, a malicious guest could cause CPU hanging, affecting the entire host. More details there.




