December 2021 XCP-ng Updates
New bugfixes and enhancement updates are available for XCP-ng 8.2 LTS.
To update, follow this guide. You can also join the discussion on our community forum. A host reboot is necessary after this update.

Summary
We usually queue non-critical fixes or improvements for a grouped release, so that you are not notified of new updates too often. This is one such grouped release.
If your hosts were up to date up until now, you may either install the updates now or skip them and wait for the next security updates to update all at once.
What changes
This update brings bugfixes, compatibility improvements, as well as some small enhancements, to a variety of components: the linux kernel, XAPI, guest templates and more.
Guest templates
The updated guest-templates-json* packages add VM templates for Debian 11, Rocky Linux and AlmaLinux.
Linux kernel
The linux kernel in the controller's domain (dom0) is updated to include several bug fixes:
- Network performance regression fixed: due to a previous security fix, the IRQs associated to virtual network interfaces (VIFs) were not balanced among CPU cores as they should be, so they were all handled by the first one, CPU0. If CPU0 would get overloaded, a performance penalty would be observed.
- Spurious kernel warnings were removed.
- Other kernel bug fixes.
This update is a backport of the fixes from Citrix Hypervisor's XS82E030 and XS82E034 hotfixes to XCP-ng's kernel.
A reboot is required for the updated kernel.
XAPI
Updated packages for the Xen API (XAPI) bring:
- USB passthrough fixes: the update fixes passing through both a PCI device and a USB device to a VM, and may also fix other USB passthrough issues that raised the same error in the logs ("usb_reset.py attach: error: argument -r: expected one argument"). This fix was contributed to the XAPI project by a member of the XCP-ng community. Well done!
- A change that we also contributed upstream and fixes WebSocket connections in Firefox. This fixes the VM console display in Xen Orchestra Lite.
- Reduced log verbosity for stunnel, to prevent
xapi-ssl.logfrom growing so fast that it could fill the/var/logpartition entirely in some cases (users from HA-lizard had reported such behaviour). - Fixed
xe vm-reset-powerstatefor VMs with GPU passthrough that are stuck in paused state. - Other fixes for rare issues (see Citrix Hypervisor's hotfix description). Note: contrarily to what Citrix did, we did not remove HTTP access to the host's web page due to a regression (that we debugged and reported to the XAPI project).
CA certificates
The ca-certificates RPM contains root certificates that may be used by OpenSSL to validate a SSL/TLS certificate. An update was necessary after the expiry of a root certificate that was used in the chain of trust of Let's Encrypt certificates. The main features of XCP-ng were not impacted, but tools such as wget would fail to download from HTTPS websites that use a Let's Encrypt certificate.
The updated ca-certificates RPM fixes that.
GRUB
The RPM package that contains our bootloader, GRUB, was updated to account for buggy UEFI firmware that is not able to boot if they can't find a bootloader at a precise location (EFI/BOOT/BOOTX64.EFI).
If you already have a working XCP-ng installation, this update will not change anything. If you have an unbootable UEFI installation of XCP-ng, booting the installation ISO in rescue mode, "chrooting" into the host's root filesystem and installing the update may fix your boot issue. Future releases of our installer will include this update directly.
xcp-featured ("fake" license daemon)
Our license daemon, who basically responds "yes, of course" for every known feature (reminder: all of XCP-ng features are enabled right from the start, without any license subscription), was updated to account for a new feature: Pool Secret Rotation.
Pool Secret Rotation (command: xe pool-secret-rotate) allows to change the pool secret shared among members of the pool to identify themselves as a members of the pool. For security reasons, you may want to rotate the secrets when an admin leaves your organization.
Small update of the host's home web page
Updated xcp-ng-release* packages bring small fixes and enhancements to the XOA quick deploy feature that is available on a host's web page.
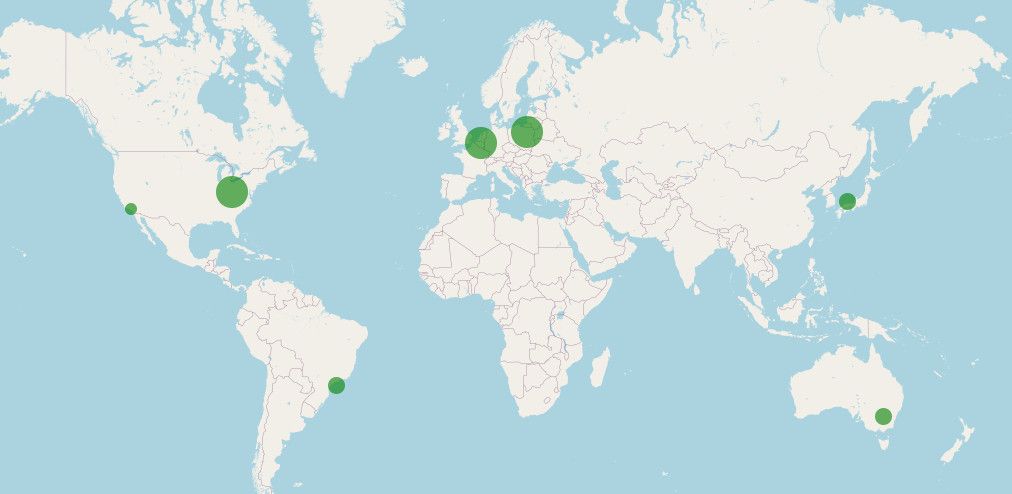
Behind the scenes: XCP-ng mirrors
Invisible to most users, our team and our mirror providers worked hard to overcome the fallouts of the expiry of the former root certificate used by Let's Encrypt, in order to maintain the compatibility of every mirror with our installer's netinstall feature, without requiring new installation images to be released.
Newer installation images will still be released in the future, which will work even without this configuration change on mirrors, but we wanted to maintain compatibility with the original 8.2 installation ISOs anyway.
If you are interested in hosting a mirror for XCP-ng, check our documentation.
Acknowledgements
The XCP-ng community was involved in many ways in the preparation of the updates described above: bug reports, debugging, tests, feedback, and even fixing bugs directly.
A big thank you to everyone!




