XSA-468: multiple Windows PV driver vulnerabilities - update now!
-
@dinhngtu said in XSA-468: multiple Windows PV driver vulnerabilities - update now!:
@conitrade-as Installing the XenServer 9.4.1 tools and rebooting (a couple times) will be enough.
The multiple reboots is the annoying part, ha... working on my systems now. I've always used https://www.xenserver.com/downloads for this.
On numerous VM's I've been installing over top of the existing drivers and within System Manager I still see
 .
.Should I just uninstall the old stuff first, then install the updated to address?
-
@conitrade-as The XAPI update was backported to 8.2.1 LTS so you could update your hosts for the new display.
@DustinB If you're coming from old XenServer tools to new, no need to uninstall.
-
@dinhngtu said in XSA-468: multiple Windows PV driver vulnerabilities - update now!:
@DustinB If you're coming from old XenServer tools to new, no need to uninstall.
Interesting, the alert is still within XOA
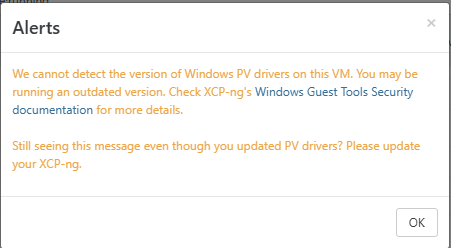 ...
... -
@DustinB Do you have the newest pool updates? The warning depends on that.
-
@dinhngtu said in XSA-468: multiple Windows PV driver vulnerabilities - update now!:
@DustinB Do you have the newest pool updates? The warning depends on that.
I have an open ticket for that.....
-
@dinhngtu On a Windows 10 VM rebooting alone did not do the trick. After 5 reboots the script still reports vulnerable devices:
.\Install-XSA468Workaround.ps1 -Scan Looking for vulnerable XenIface objects Found vulnerable object XENBUS\VEN_XSC000&DEV_IFACE\_ Found vulnerable object XENBUS\VEN_XSC000&DEV_IFACE\_ Looking for vulnerable XenIface WMI GUIDs Found vulnerable WMI GUID 1D80EB99-A1D6-4492-B62F-8B4549FF0B5E Found vulnerable WMI GUID 12138A69-97B2-49DD-B9DE-54749AABC789 Found vulnerable WMI GUID AB8136BF-8EA7-420D-ADAD-89C83E587925 Found XenIface vulnerability, it's recommended to run the script TrueRunning
.\Install-XSA468Workaround.ps1works as expected. After another reboot nothing is reported as being vulnerable anymore.On a Windows 2019 Server I saw the behaviour you described: Installing the tools and a reboot was enough.
-
On another Windows 10 host it worked. What was different: I saw the message box "Tools have been installed successfully". May be that makes a difference?
-
@conitrade-as I saw that on your Windows 10 VM, the "Manage Citrix PV drivers via Windows Update" option is enabled. That one might have needed a Windows Update to install the fixed drivers. Do you have that option enabled in other VMs?
-
@dinhngtu On the machine where it worked, the option "Manage Citrix PV drivers via Windows Update" was not enabled. Seems that my older BIOS Windows 10 VMs have that option enabled. On all UEFI VMs the options is disabled.
As I wanted to go and check that is present in the templates, I realized that the Windows Templates are gone from Xen Orchestra v5.106.4???
-
@conitrade-as said in XSA-468: multiple Windows PV driver vulnerabilities - update now!:
As I wanted to go and check that is present in the templates, I realized that the Windows Templates are gone from Xen Orchestra v5.106.4??
Can confirm all templates for Windows are missing on 5.107.0 as well.
-
@conitrade-as @DustinB Thanks, reported the template issue to XO team.
-
Here is another interesting fact: After installing the new tools (v.9.4.1) my static routes in Windows were all gone.
 Definitively a good way to loose connectivity to your domain controller. And that's why you have good monitoring and store things in Ansible et al. ...
Definitively a good way to loose connectivity to your domain controller. And that's why you have good monitoring and store things in Ansible et al. ... 
-
@conitrade-as said in XSA-468: multiple Windows PV driver vulnerabilities - update now!:
Here is another interesting fact: After installing the new tools (v.9.4.1) my static routes in Windows were all gone.
 Definitively a good way to loose connectivity to your domain controller. And that's why you have good monitoring and store things in Ansible et al. ...
Definitively a good way to loose connectivity to your domain controller. And that's why you have good monitoring and store things in Ansible et al. ... 
Statically assign, but keep your DHCP server with reservations to address these types of issues

-
@DustinB Did run usr/bin/create-guest-templates but tepmlates are gone here also.
-
@manilx said in XSA-468: multiple Windows PV driver vulnerabilities - update now!:
@DustinB Did run usr/bin/create-guest-templates but tepmlates are gone here also.
I did not, I'm in the middle of an AV/EDR migration and this way added to the list of things to touch while I was on the systems.
To me the templates are a minor inconvenience as we aren't constantly adding VMs.
-
@DustinB Not IP assignments, I am talking about static routes. See e.g. https://learn.microsoft.com/en-us/powershell/module/nettcpip/get-netroute
-
@conitrade-as said in XSA-468: multiple Windows PV driver vulnerabilities - update now!:
@DustinB Not IP assignments, I am talking about static routes. See e.g. https://learn.microsoft.com/en-us/powershell/module/nettcpip/get-netroute
Okay.... what...
-
Hi! Regarding the templates issue, we're working on a fix on branch
pierre-fix-xsa468-testmaster. Would anyone having the issue be available to test it? -
@pdonias Sure thing. I can test it in my test environment.
-
Just did a couple more tests. Here are my findings:
- Upgrading the tools from v9.3.3 to v9.4.1 does preserve the routing table.
- Upgrading the tools from v9.2.1 to v9.4.1 does not preserve the routing table.
Here are a couple of powershell commands used for testing:
Get-NetRoute -PolicyStore PersistentStore Get-NetAdapter New-NetRoute -DestinationPrefix "10.10.0.0/24" -InterfaceIndex <ifIndex> -NextHop 10.10.0.254
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login