-
@stormi It installs and runs....
The "help" does not mention the user-agent option.
-
@Andrew That's because
installis a sub-command:secureboot-certs install -h.Anyway, if download fails (you can test by using "test" as the user agent for example), the option will be mentioned.
-
To me, this
uefistoredupdate is ready, but I'll group it with the next updates.Test feedback remains welcome.
-
New security update (xen)
Impact: when the conditions are met (roughly: CPU Model, PV guest + PCI passthrough or race condition exploitation), an attacker in a malicious VM may escalate privilege and control the whole host.
Upstream (Xen project) references: XSA-401 and XSA-402
Test on XCP-ng 8.2
From an up to date host:
yum clean metadata --enablerepo=xcp-ng-testing yum update xen-dom0-libs xen-dom0-tools xen-hypervisor xen-libs xen-tools --enablerepo=xcp-ng-testing rebootVersions:
- xen-*: 4.13.4-9.22.2.xcpng8.2
What to test
Normal use and anything else you want to test. The closer to your actual use of XCP-ng, the better.
Test window before official release of the updates
~2 days.
-
@stormi Update worked fine and no problems so far. Did the usual tests to create, move, snapshot, backup and restored some Linux and Windows VMs.
-
@stormi I've had it running for 24 hours on several active machines doing the usual jobs. Seems good.
-
Same here

-
Update released (xen + uefistored). Thanks for your tests!
Blog: https://xcp-ng.org/blog/2022/06/13/june-security-update-1/
-
New security update (xen, Intel CPUs)
Xen is being updated to mitigate hardware vulnerabilities in Intel CPUs.
- Upstream (Xen project) advisory: XSA-404
- Citrix Hypervisor Security Bulletin (which also covers vulnerabilities that we already fixed in the previous update): https://support.citrix.com/article/CTX460064/citrix-hypervisor-security-update
Impact of the vulnerabilities - I'll quote Citrix' security team here: "may allow code inside a guest VM to access very small sections of memory data that are actively being used elsewhere on the system"
Test on XCP-ng 8.2
From an up to date host:
yum clean metadata --enablerepo=xcp-ng-testing yum update xen-dom0-libs xen-dom0-tools xen-hypervisor xen-libs xen-tools --enablerepo=xcp-ng-testing rebootVersions:
- xen-*: 4.13.4-9.23.1.xcpng8.2
What to test
Normal use and anything else you want to test. The closer to your actual use of XCP-ng, the better.
Test window before official release of the updates
~2 days.
-
@stormi
This seems to be working well on my test pool. -
Same here

-
@stormi The initial update worked fine on my playlab (two Dell Optiplex 9010, Intel i5-3550 CPU, Synology shared NFS storage)
, but I can not migrate VMs between hosts anymore. Neither XO from third party script (commit 395d8, xo-server 5.96.0, xo-web 5.97.2) nor XCP-ng Center 20.04.01 work.Edit: After a complete (bare metal) restart of hosts and storage systems, everything works as expected (create, migrate, start/stop, snapshot of VMs), so I can only blame myself
-
@stormi The update has been OK for me on a bunch of standard machines (older Intel/AMD) over the last day. Normal VM operation, migration, backups, reboots, etc.
I'm having problems with cross host VxLANs, but I can't blame the update for that. I reinitialized the XO SDN plugin and it's working again. It may have something to do with changing pool masters and rebooting the hub server.
-
The update is published. Thanks for your tests!
Blog post: https://xcp-ng.org/blog/2022/06/27/june-2022-security-update-2/
-
Thanks for the new update!
We're trying to determine if we are vulnerable to this. In https://xenbits.xen.org/xsa/advisory-404.html I see:
Per Xen's support statement, PCI passthrough should be to trusted
domains because the overall system security depends on factors outside
of Xen's control.
As such, Xen, in a supported configuration, is not vulnerable to
DRPW/SBDR.
Does this mean we are not vulnerable to XSA-404 if we do not use PCI Passthrough?
Cheers,
Niels -
@NielsH DRPW and SBDR are related to MMIO (and thus PCI Passthrough), but there are other vulnerabilities that are not related to it.
-
@stormi said in Updates announcements and testing:
@NielsH DRPW and SBDR are related to MMIO (and thus PCI Passthrough), but there are other vulnerabilities that are not related to it.
Okay, thanks. We have to update it than sadly, heh.
Cheers! -
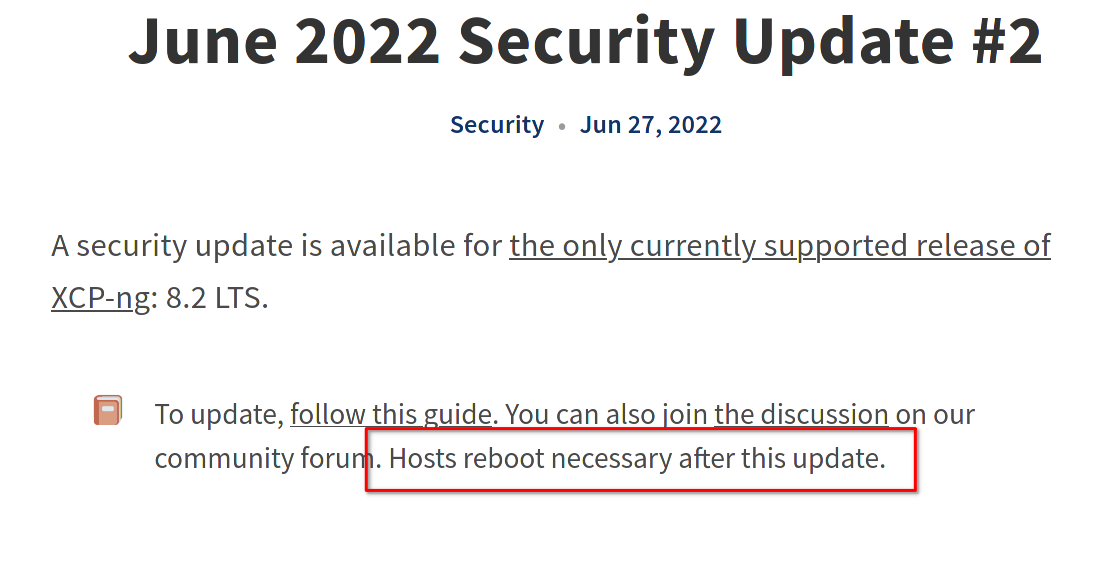
Hi, I've just applied the May and two June security updates (total of 8 patches) to a test box, no problems. But before I try these on the live pool: can anyone tell me if a reboot is required? The blog posts referenced do not mention this.
-
@normanghenderson They do

-
@stormi Doh. How did I miss that?

Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login