XCP-ng 8.3 updates announcements and testing
-
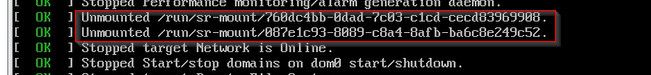
In my case, I gave the command to shut down all hosts, and the master "made it" first. The other hosts then got "stuck" at this point for a very long time:
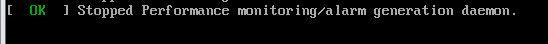
EDIT: Apparently waiting for umount:
-
@abudef In case of a shutdown, I turn off the secondary servers first. Once they are off, I shut down the primary server. This ensures that if the secondary servers have information to send to the primary, they can do so, whereas otherwise, they can wait to shut down.
In case of a pool reboot, I reboot the primary server first, and once it is accessible, I reboot the secondary servers.
-
@gduperrey Of course, the order matters. Now everything seems to be clear.
-
New security and maintenance update candidate for you to test!
A new security vulnerability, XSA-480, has been detected and fixed for xen.
Security updates
xen: A vulnerability has been discovered on x86 Intel systems with EPT support, where unintended host or guest memory regions can be accessed from a VM's memory cache under any workload. This can lead to privilege escalation, denial of service (DoS) attacks affecting the entire host, or information leaks.
On XCP-ng 8.3, x86 HVM/PVH VMs can leverage this vulnerability.
There are no mitigations.
A VSA was also published by our security team: https://docs.vates.tech/security/advisories/2026/vates-sa-2026-005/
Maintenance updates
We are taking this opportunity to release an update for
ipmitoolfollowing some feedback from our users regarding the display of an error message in Xen-Orchestra, with certain models of DELL servers, in relation to the commandipmitool lan print.Test on XCP-ng 8.3
yum clean metadata --enablerepo=xcp-ng-testing,xcp-ng-candidates yum update --enablerepo=xcp-ng-testing,xcp-ng-candidates rebootThe usual update rules apply: pool coordinator first, etc.
Versions:
ipmitool: 1.8.19-11.2.xcpng8.3xen: 4.17.6-5.1.xcpng8.3
What to test
Normal use and anything else you want to test.
Test window before official release of the updates
~2 days
-
@gduperrey No issues to report on my test systems.
-
Thank you everyone for your tests and your feedback!
The updates are live now: https://xcp-ng.org/blog/2026/03/19/march-2026-security-updates-for-xcp-ng-8-3-lts/
-
@gduperrey reboot necessary?
-
@manilx Yes, as written

-
@stormi didn't see that (my old eyes)... guessed so anyway

-
When applying updates at work. I started with first pool and choose the rolling pool updates and ran into issue after fist host came back up the second host didnt enter maintenance mode and the operation appeared to have just stopped. I then manually put host 2 in maintenance mode and applied updates. Once updates finished it restated the tool stack and took the host out of maintenance mode. I put it back into maintenance mode and rebooted the host. Once it came backup no migration occurred as expected to bring vms back to host2.
Moved on to pools 2 and 3 and just did everything manually. Each time load balance appears to be broken now just like home lab.
I have rebooted XOA deleted load balance config. rebuilt using different name and still no load balance.
Once manually migrated vms back over to second host in all three pools all seems ok.
-
@acebmxer Hello,
What you're describing sounds more like an RPU issue with Xen-Orchestra than a problem related to XCP-ng updates. But I could be wrong

However, since these updates affect Xen, a reboot was clearly indicated in our procedure. So a simple restart of the toolstack isn't enough. You did the right thing by rebooting afterward.
Are you using XO Appliance or from source?
If it's XO Appliance, you can open a ticket to ask for help analyzing the situation and see if anything in the logs or configuration explains this behavior.
If it's from source, for the same issue, I would suggest you start a separate thread on the forum so other users can help you with the analysis

In any case, it's great if your pool is working in the end

-
-
@acebmxer I invite you to open a ticket through the support ticketing system.
I do not connect remotely myself and I am also unable to provide support for Xen-Orchestra.
-
New security update candidate for you to test!
A new security vulnerability has been detected and fixed for xen.
This was introduced by an upstream commit, and detected before the Xen Project did any new release. Therefore this does not impact any upstream release, and there is no Xen Security Advisory this time. But that change was backported into XCP-ng
xenpackage, therefore XCP-ng is impacted.
Security updates
xen: Fix a security issue where insufficient memory sanitization during guest creation can lead to information leakage from previous guests and potential privilege escalation
Test on XCP-ng 8.3
yum clean metadata --enablerepo=xcp-ng-testing,xcp-ng-candidates yum update --enablerepo=xcp-ng-testing,xcp-ng-candidates rebootThe usual update rules apply: pool coordinator first, etc.
Versions:
xen: 4.17.6-5.2.xcpng8.3
What to test
Normal use and anything else you want to test.
Test window before official release of the updates
~2 days
-
@gduperrey Installed on my usual round test hosts. No issues to report so far! With such a small change i wasn't expecting anything to go wrong!
-
@gduperrey
All good so far -
@gduperrey Up and working on several Intel pools.
-
@gduperrey Seems to be working well on my test systems.
-
How many of these are critical? I haven't even had time to apply the last round of patches to either lab or production.

-
Thank you everyone for your tests and your feedback!
The updates are live now: https://xcp-ng.org/blog/2026/03/26/march-2026-security-updates-2-for-xcp-ng-8-3-lts/
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login