@BenjiReis
is there another SDN controller connected to your pools? (not necessarily an XO SDN controller) that would override the certificates of XO?
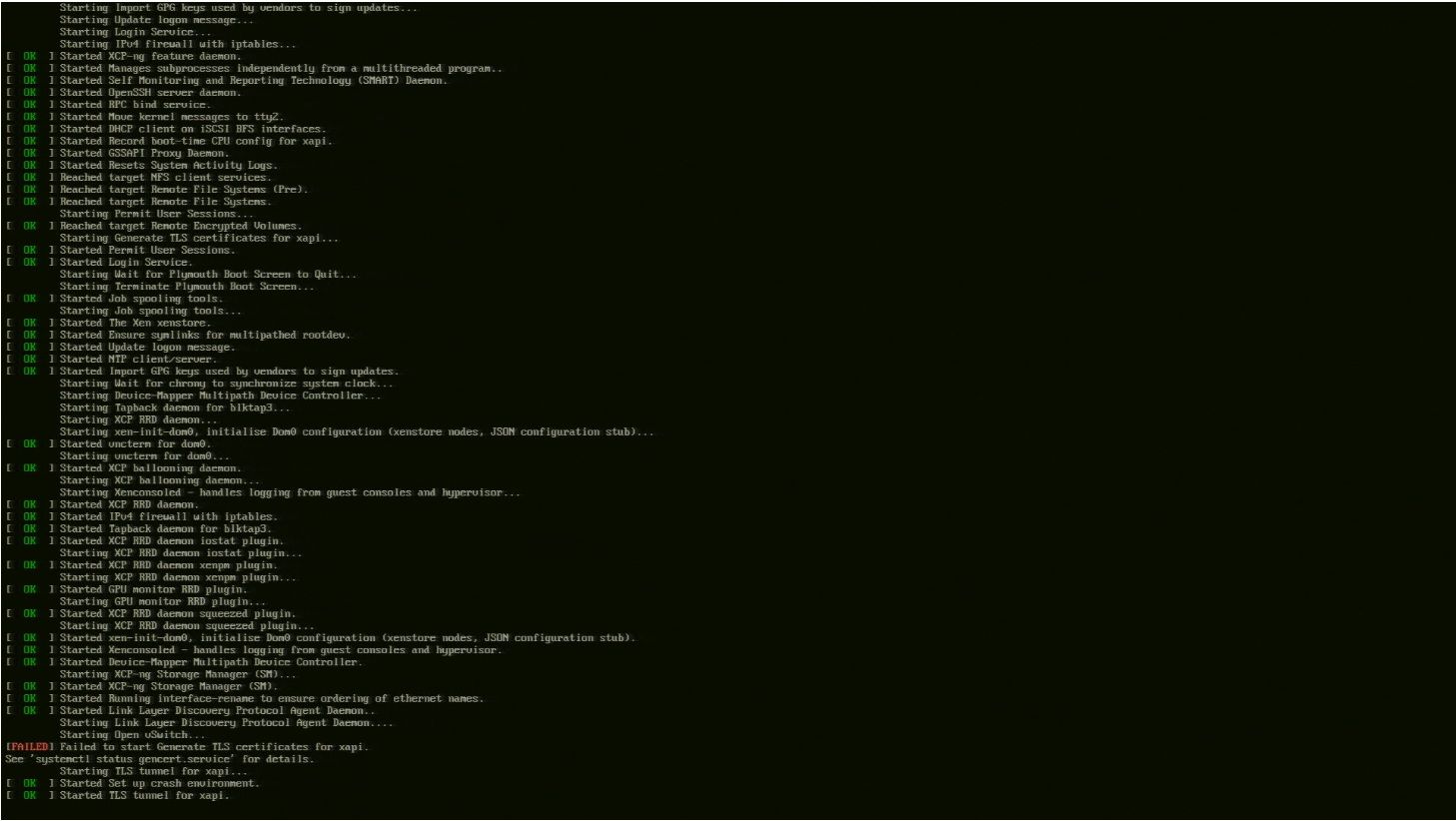
None. I have just done a clean install of Xcp-NG 8.3 beta 2
Are there any XAPI error (in /var/log/xensource.log) when you restart your VM?
I just ran cat /var/log/xensource.log | grep error and got the following :
xapi: [error||376 |xapi events D:exxcfeaxxbxx|xenops] events_from_xapi: missing from the cache: [ 1xx05x9-x65x-xxxxxxx]
Are the certs copied to the xcp-ng hosts in a pool ?
Is there way to delete all SDN certificates from hosts so that new ones are copied automatically ?
Update :
I don't think certificates are at fault. Checked /etc/stunnel/certs and the certificates are same in all hosts
New Error while re-creating VxLAN (this time non encrypted)
xo:xo-server:sdn-controller:ovsdb-client ERROR No result for select {
columns: [ 'name', 'options' ],
table: 'Interface',
where: [ [ '_uuid', '==', [Array] ] ],
host: 'xxxxx-2'
}
I'll try the GRE networks now